Problem: How to troubleshoot AD integration issue in Mobility using Apache Directory Studio?
Cause: When onboarding a customer in EMM, the AD integration could fail due to various reasons. This could include LDAP port issue, incorrect or unavailable IP address, incorrect security context, incorrect credential, improper SSL set up, etc.
Resolution: Although ldp.exe gives you the option to troubleshoot AD and EMM integration issue, it might be best to troubleshoot this issue using Apache Directory Studio as this takes encryption in context as well. Please use below steps to perform this test:
1. Download the Apache Directory Studio on your Kaseya Server:
- http://directory.apache.org/studio/downloads.html
- http://directory.apache.org/studio/download/download-windows.html
2. Add a new connection:

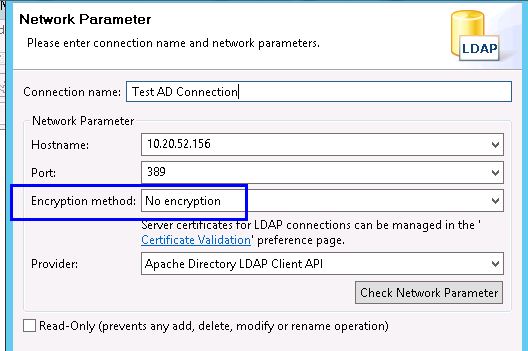
3. Complete the connection details - you can choose startTLS encryption here.
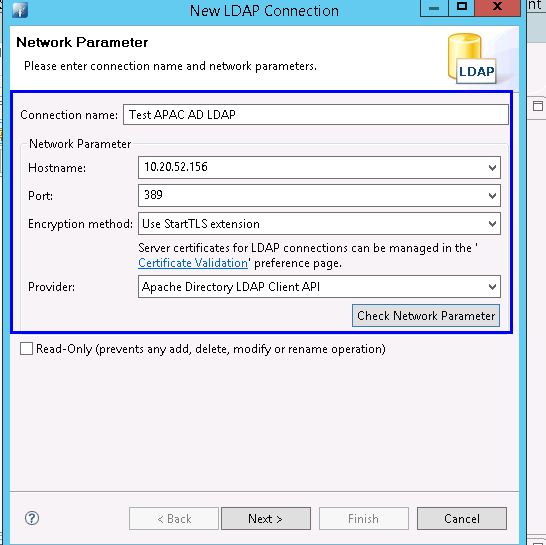
4. Test if the hostname resolves properly or not by clicking Check Network Parameter. If you see any errors, expand additional information to see more details.
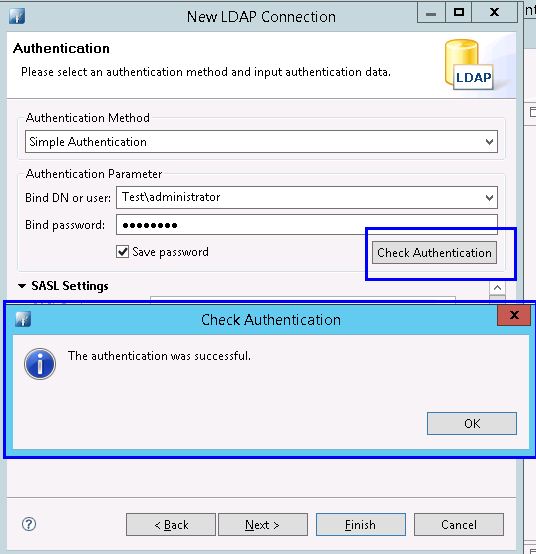
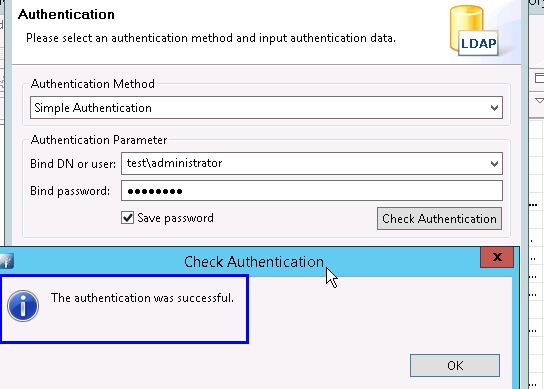
5. Please proceed ahead with authentication:
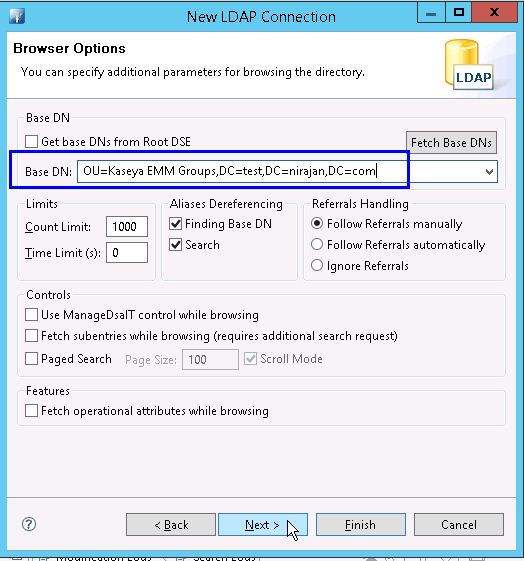
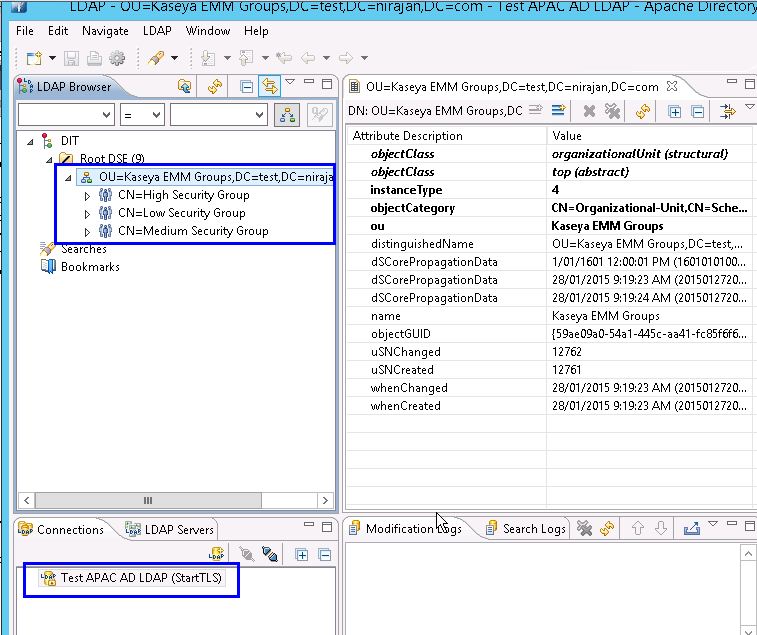
6. If all completes you will see 3 security groups that you had created as needed by Kaseya under that OU that you have defined in base DN
Troubleshooting a Failed Connection: The connection to the AD server may fail if:
- Apache Directory Studio cannot reach the AD server.
- The port entered in Apache Directory Studio is incorrect.
- The encryption method in Apache Directory Studio does not match the encryption method of the AD server.
To ensure that you can reach the server, execute the following command and verify that you receive a response:
ping 10.20.52.156
To verify that the server uses the port that you entered in Apache Directory Studio, execute a command similar to the following and verify that you receive a connected status:
telnet 10.20.52.156 389
Authentication with the bind DN or username may fail if:
- The bind user entered does not exist in AD.
- The bind user entered does not have permission to browse LDAP.
- The DN or username is not formatted properly.
Certificate Issue: You will see below error if there is no certificate installed in AD machine:
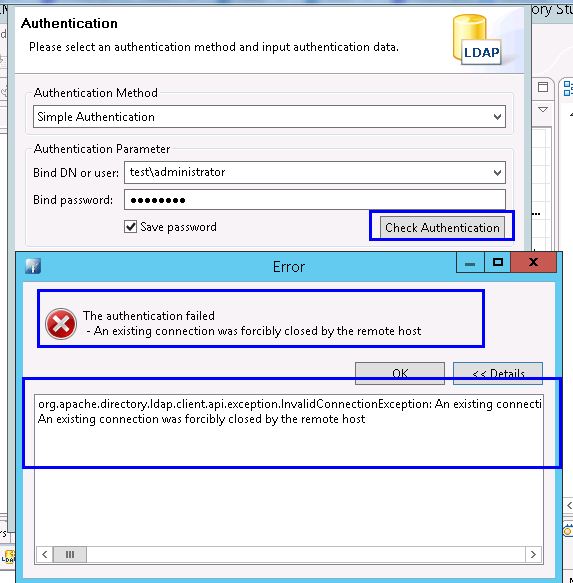
To confirm that above error is not coming due to credential issue, please click OK, go to previous menu, choose encryption to be none, click next and check authentication again. If the credential is OK, you will see test pass. This will confirm that the issue is with certificate/encryption
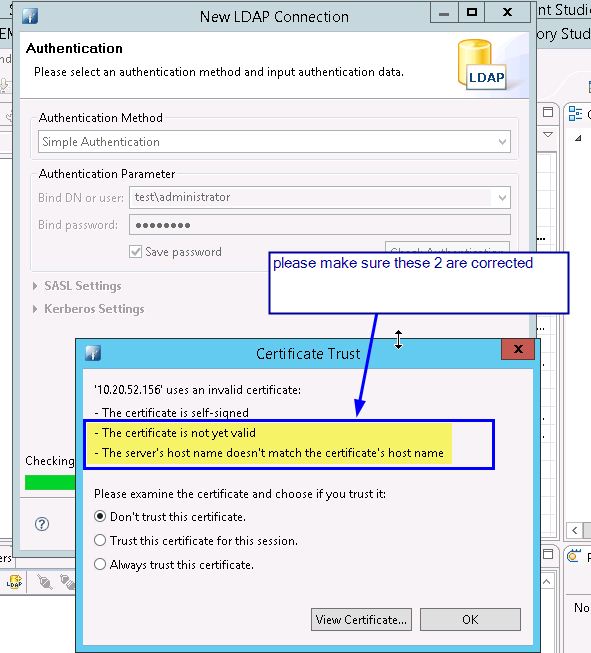
Note: You may however still see an issue with Encryption even when self signed certificate is used. Please ensure you correct below highlighted ones. If it only prompts for self signed, ignore it and proceed ahead:
Reference:
- https://jamfnation.jamfsoftware.com/article.html?id=224
- https://www.ibm.com/developerworks/community/blogs/ibm-bi-capabilities/entry/using_apache_directory_server_apacheds_based_ldap_to_secure_ibm_cognos_10_2_bi_environment?lang=en
Applies to: VSA 9.0, 9.1, 9.2, 9.3, 9.4.