QUESTION:
How do I troubleshoot the Oracle monitor tests that are not working?
RESOLUTION:
- In order for Traverse to monitor the Oracle database, please make sure the Oracle database supports remote network (SQL*net) queries
- Clients/applications to test remote connectivity (please test from the DGE or DGEx server that will be monitoring the Oracle database):
-- TNSPING
-- TOAD
-- SQL*Plus - It has been determined that there may be connection issues with specific versions Oracle Database. One known version that may have issues with Traverse Oracle monitoring is 12.1:
"In 12.1, the default value for the SQLNET.ALLOWED_LOGON_VERSION parameter has been updated to 11. This means that database clients using pre-11g JDBC thin drivers cannot authenticate to 12.1 database servers unless theSQLNET.ALLOWED_LOGON_VERSION parameter is set to the old default of 8.
This will cause a 10.2.0.5 Oracle RAC database creation using DBCA to fail with the ORA-28040: No matching authentication protocol error in 12.1 Oracle ASM and Oracle Grid Infrastructure environments."
-- Set SQLNET.ALLOWED_LOGON_VERSION=8 in the oracle/network/admin/sqlnet.ora file
Source: http://stackoverflow.com/questions/24100117/ora-28040-no-matching-authentication-protocol-exception - Review Oracle configuration files:
sqlnet.ora
tnsnames.ora
listener.ora - At the time of this writing, the JDBC driver for Oracle Database supports the following encryption implementations within sqlnet.ora:
RC4_256
RC4_128
RC4_56
RC4_40
DES
DES40
- A Wireshark capture can provide additional troubleshooting information to determine what part of the connection attempt is having issues.
To get started on reviewing the Wireshark capture yourself:
-- Filter on the listener port, in my example I am using port '1521' (e.g. tcp.port == 1521)
-- Once filtered, make sure to decode the information on port '1521' as TNS. To do this, right-click on one of the packets and select 'Decode As'. Set port '1521' to TNS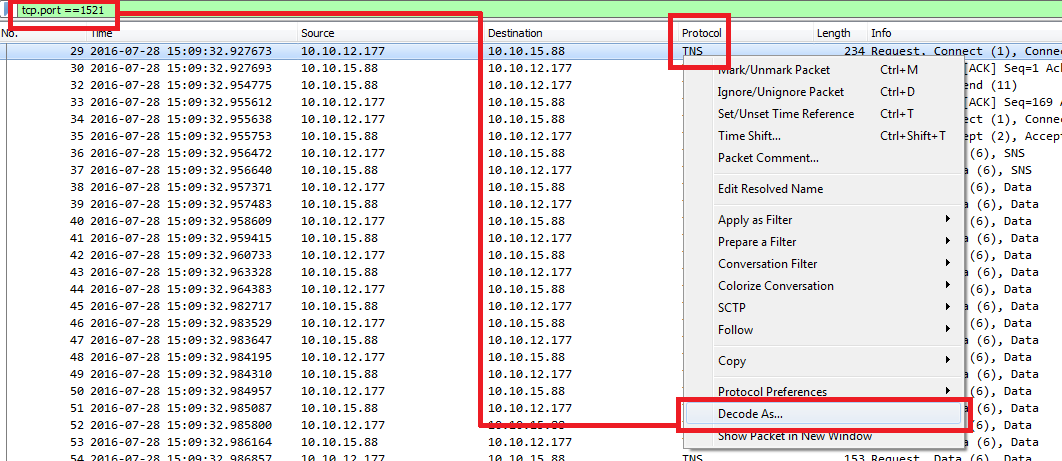

--If assistance is required in reviewing the Wireshark capture further, support is more than happy to assist. Please include the Wireshark capture upon creating a support ticket
APPLIES TO
All versions of Traverse
REFERENCE
None